I don't know, but I can guess... One of the most common technical tasks I'm asked to help with is getting a wireless printer back on the network. Seems that many wireless printers 'fall off' the wireless network every 6-18 months. Why? I am not certain, but my techie instincts tell me that the driver software that's written for printers is getting less attention from quality control lately, and I don't predict printer companies will fix this problem soon.
My advice to you is to remove and re-add your printer on your Windows or Macintosh PC. This alone solves this problem 50% of the time.
1 Comment
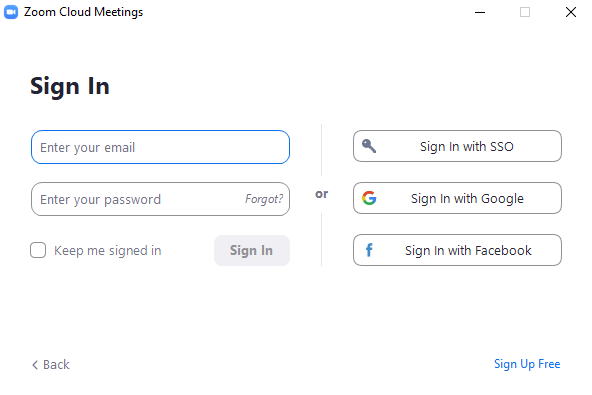
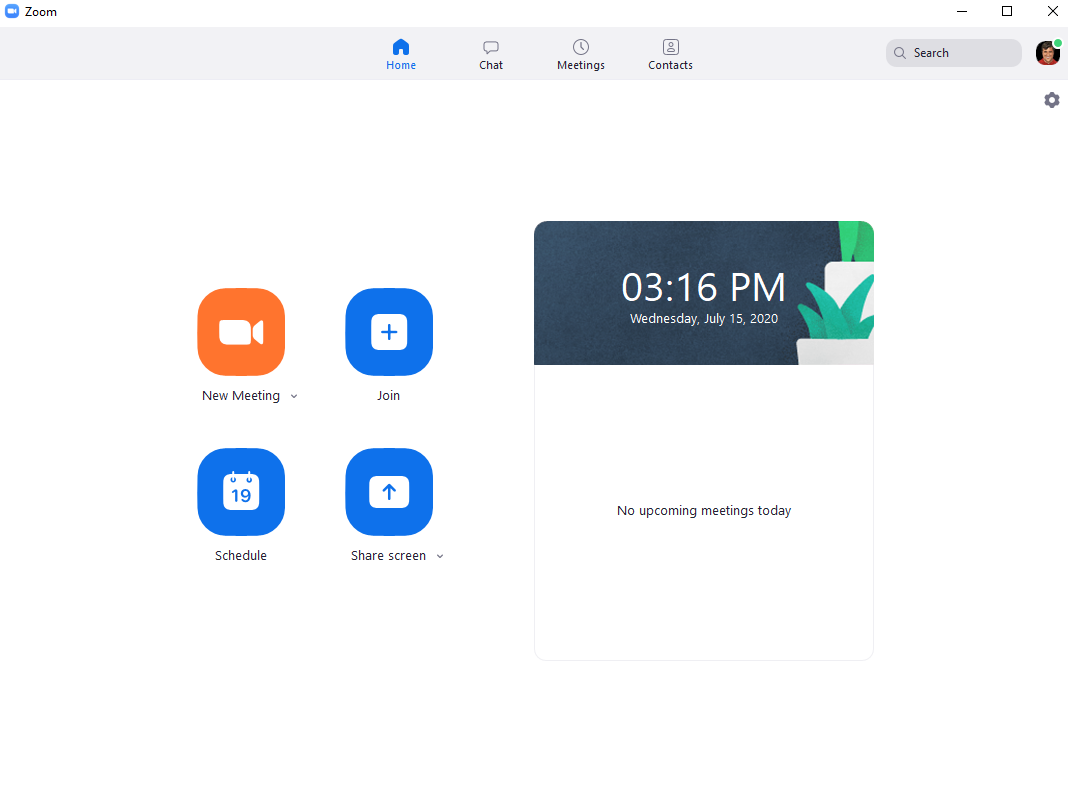
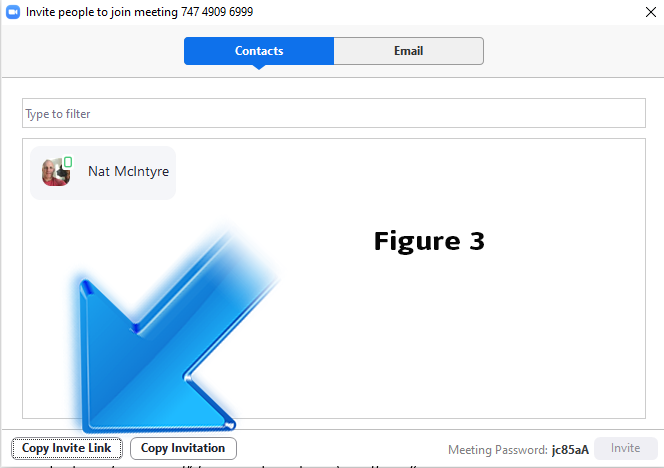
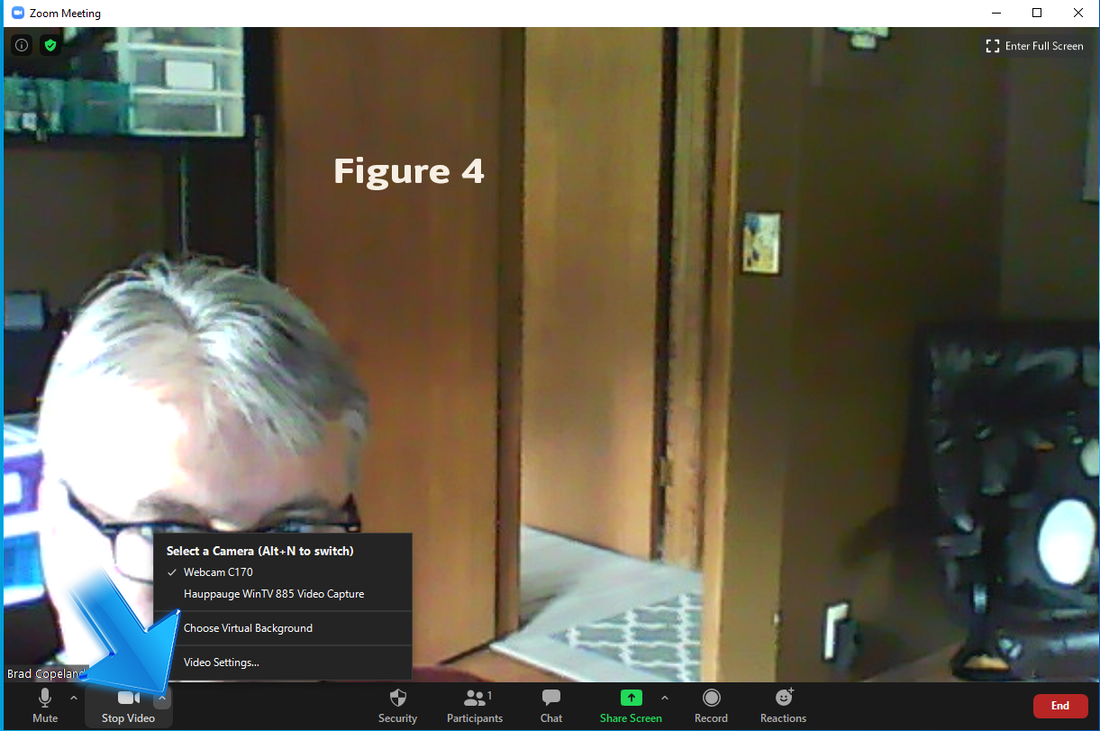
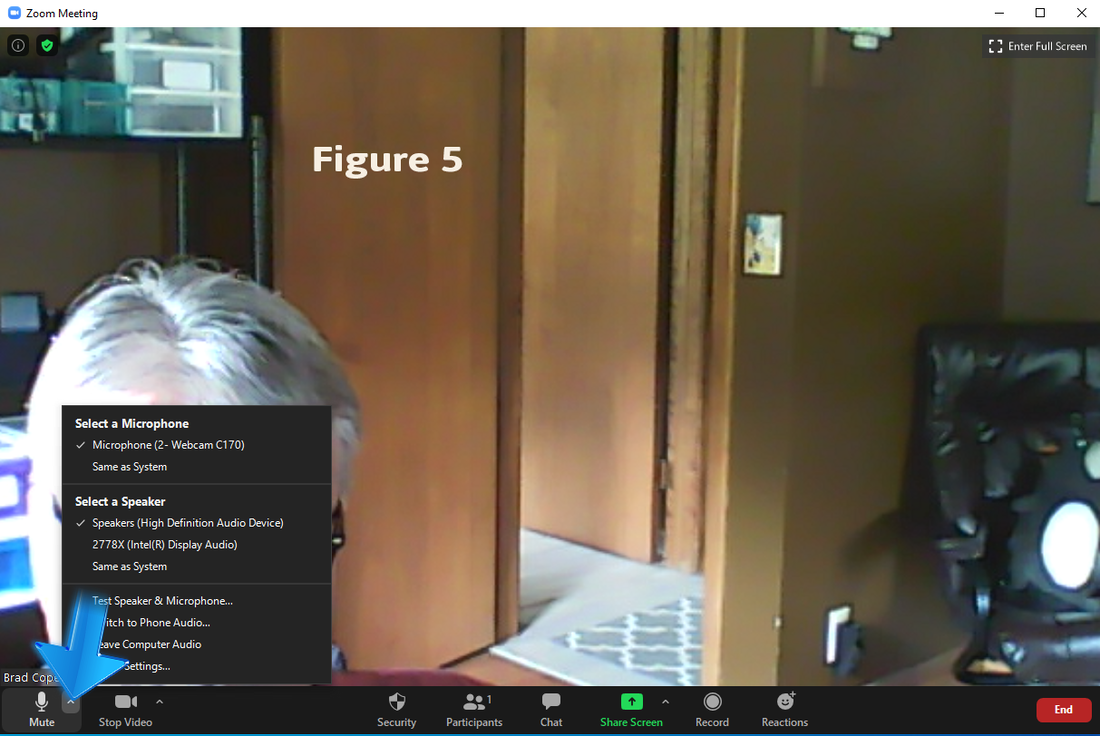
Zoom is the winner of the videoconferencing apps, so it is best you understand some basic steps, basic concepts, and be prepared for oddities. Account You’ll need an account to use Zoom and creation of any account requires an email address and a password of your choice. Visit http://www.zoom.us to create an account. Download and Install Zoom is not a Web-based app, so you’ll need to download and install the Zoom program to use it. Here is the URL to download Zoom: https://zoom.us/download#client_4meeting Logging In This is what you’ll see when you’ve successfully installed the Zoom app and it’s ready for you to log in. The Initial Screen This is the initial screen you’ll see after you’ve logged in. This is a basic tutorial, so let’s only worry about the ‘New Meeting’ and ‘Join’ buttons. New Meeting You’ll use the New Meeting button to create a meeting for others to join. Join The Join button allows you to join a meeting, but only if you know the Meeting ID of the meeting. This Meeting ID is probably in an email somewhere. Zoom meeting IDs look like 732 4566 7899 (3 digits, then two sets of 4 digits). Oddities -When you get an invitation in your email, it will have a (relatively long and complex) URL to click on to join a meeting. That’s not the odd part. The odd part is that when you click on the link, it will pop up your default browser (e.g., Chrome or Firefox) and then start the Zoom app. Just let that happen and click yes when it prompts you to open the Zoom app. -Inviting people to an existing meeting is cumbersome. If you have a meeting started and you want to invite people to your meeting, you’ll click participants (see figure 2), then click invite. That’s where it gets messy. After clicking invite, you’ll see figure 3, where I suggest you choose ‘Copy Invite Link’ and paste it into an email to desired participants. -The invite box will remain on top of everything until you close it, which is a bit odd. You may want to close it before emailing the invite link. Sound and Video -You’ll need to have video (your Webcam) and sound (speakers and microphone) configured properly to fully participate in Zoom meetings. You may have more than one camera and you might have more than one microphone on your computer. Figure 4 shows where you’d choose a Webcam and figure 5 shows where you would choose speakers and microphone. I hope this gets you Zooming with confidence. The first time using Zoom may feel daunting. Give yourself a few minutes to get things going. Feel free to drop me a line if you have questions.
Thanks, Brad I suggest purchasing a laser printer rather than an ink-jet printer, but if you're going to go cheap, I suggest Canon. There are three primary brands of ink-jet printer and they are HP, Epson, and Canon. Epson is the worst, Canon is (reliably) the best, and HP is in between. Here are the criteria I use to judge an ink-jet printer:
I will assume that if you're buying an ink-jet printer, you're probably not buying it for a business application. That being assumed, then one of the most compelling reasons to buy a Canon ink-jet printer is the ease of setup and use. Even high-quality HP printers have inscrutable interfaces. HP printers have too many buttons, too many choices, and the symbolism used by HP is arbitrary. Interface complexity is an area where HP may, depending on the model, be worse than Epson. With any ink-jet printer, I suggest assuming it will last 2.5 years. What does this mean in practice? If you are having any, and I mean ANY, problems (e.g. won't connect to WiFi, trouble picking up paper, streaky printing) with your ink-jet printer and it is 2.5 years old or older, do not buy more ink for it, just get a new one. The short answer: If you have to ask, there is a risk that a Chromebook is not for you.
The nitty gritty problem with Chromebooks is the software restriction. Most users would (at least eventually) be able to get used to the other differences and shortcomings of a Chromebook, but the software restriction problem would likely be a deal-breaker for most users. The only software that will work with a Chromebook is (a) Web-based software (e.g., Google Docs, browser-based games) and (b) software available at the Google Play Store. The odds that you will one day regret not getting a Windows or a Macintosh computer are very high. Maybe you'll get your scanner working with your Chromebook, but then you'll run into the limitation of not being able to use your favorite software to crop or otherwise fix the photos you've scanned. I would liken a Chromebook to a higher-functioning tablet. So, you might be a candidate for a Chromebook if you accept that it will mostly be for consumption (watching movies, reading emails) as opposed to creation (creating movies, creating documents to attach to email). If you're on the fence about getting a Chromebook, I will advise you on it for free. With just a couple of minutes on the phone, I'll be able to tell you whether you'll likely encounter problems or not. 612-423-5370 Tech glossary
*The analogies here (like any tech analogy) are somewhat incomplete and inappropriate, but should suffice. Router vs. Modem vs. Gateway A router is the device that allows sharing of a single Internet connection with many devices (through wired and wireless) and helps keep the bad guys from seeing your device or devices as nakedly on the Internet. A modem is a much less intelligent device in comparison to a router. All a modem does is turn a phone (DSL) or cable line into something a router can use. Ironically, most of you have a ‘gateway’ device in your homes. A gateway is both a modem and a router, and except for Comcast’s gateway, most of them (Centurylink’s, Mediacom’s) do not do a great job as a router. ISP Your ISP is your Internet Service Provider. In suburban Minnesota, your ISP is most likely to be Comcast or Centurylink, and if you go out of the city, it might be Frontier or Mediacom. This is the company that has or creates a line to your home or business that will send Internet to a modem or gateway device. There are usually only two choices of ISP in any specific location, and sometimes both are undesirable choices. An ISP may provide a speedy, reliable Internet connection, but have terrible customer service or (less common these days) deceptive billing practices. Centurylink is known for having an ‘entry level’ performance level that is insufficient for some user’s needs. Account An account is always at least a username (usually an email address) and a password. Some more secure accounts require more than a username and password. For contrast, when connecting to a WiFi network, you usually only need to know one thing: the password. You usually do not need to create or log into an ‘account’ to connect to a WiFi network. On the other hand, if you want to buy something on Amazon or purchase tickets to a sporting event, you’ll need an account. VPN A virtual private network (VPN) is any network connection that is encrypted. The benefit of a VPN is that if a bad guy somehow captures the data you’re sending or receiving, he won’t be able to make heads or tails of it. The drawbacks are (a) the complexity in using a VPN and (b) possibly a slower connection speed. Malware Malware is malicious software. Malware could be spyware, adware, keyloggers, trojans, viruses, or anything that is unwanted software that was designed with less-than-helpful intent. The sad truth in 2019 is that there is no single security software tool that stops all malware, at least on a PC. In addition to anti-virus, you’re advised to also run manual malware scans Operating system software vs. application software Operating system (OS) software is the house and application software is the furniture, appliances and people who live in the house. An OS has a foundation (interface), temperature controls, plumbing (often 3rd party tools, like Ccleaner), doors (shortcuts), and windows. But, the OS is useless without application software, just as a house is (relatively) useless without furniture, appliances and people. All OSs come with ‘native’ application software, such as Wordpad on Windows and Notes on a Macintosh. Robot or ‘bot’ In the world of technology, a robot is considered anything that has more than rudimentary artificial intelligence (A.I.). Technically, your thermostat has A.I. because it’s smart enough to regulate the temperature in your home even with weather changing outside of your home. But that’s rudimentary A.I. The confusion comes when a Captcha asks “Are you a robot?” and you picture a physical robot sitting at your computer. See, a robot (or ‘bot’) can be any truly intelligent, adaptable A.I., including a software program. And yes, there are software programs that will fake a login process. Webmail vs. email client software Webmail is when you check/manage your email from a browser (e.g., Chrome), and an email client is software specifically for email. Email client software often also manages contacts and your calendar (e.g., Outlook), but you cannot ‘surf the Web’ from any email client. Webmail is convenient, portable, and familiar, whereas email clients are productive, powerful and, in the case of Outlook, fussy and buggy. Memory vs. hard drive (or SSD) Memory is comparable to your workspace/short-term recall and your hard drive (or SSD; we’ll just call it hard drive henceforth) is more like a file cabinet. When you ‘add more memory’ to your computer, you’re making it more capable in a general sense. When you add more hard drive space, you’re making it so you can store more stuff. Browser A browser is a software tool that allows you to visit Websites. Lots of Websites have apps that allow you to use their services without visiting a Website, but most of them started out only having a Website (e.g., Facebook, Amazon, Match, Ebay). Only a browser can visit www.website.com (substitute whatever URL you want for website.com). It may seem you can open a Website from a text message, but a URL in a text message will open a browser. The common browsers are Chrome, Firefox, Edge, and Safari. Which one is the ‘best’? That is an unanswerable question for two reasons: (a) sometimes it’s just preference and familiarity and (b) the browser with superior features, stability, speed, and security changes from year to year. File vs. Folder vs. Drive One of the most annoying vestigial naming conventions in technology is to call an individual, usable item a ‘file.’ When you’re watching a detective TV show, and someone asks “Get me the file on the accused,” you don’t picture one item, you picture a group of various items (e.g., photos, plastic bags with evidence, reports, phone logs) stored in a manila folder or a box. Well, on a PC, a Mac, an iPhone, or a Droid, a ‘file’ is one item (e.g., a photo, a PDF, a system file, or a video). Most files on a computer (a phone and a tablet are computers) are stored in folders, and those folders are all stored on a drive of some sort (usually your primary hard drive). Hacker vs. scammer A hacker is someone with mastery of software, whereas a scammer does not necessarily have to have a high level of skill or knowledge with software. Hackers must work hard to gain their skills and tend to be more focused in their targeting, whereas scammers are lazy and tend to cast a wide net that’s easier to spot. For further contrast, a hacker will actually take over a Facebook account, whereas a scammer will create a new Facebook account that looks like yours and try to get people to send him or her money. The former is much more challenging than the latter, and you are much more likely to be victimized by a scammer than a hacker. Phishing email Phishing is digital ‘fishing’ through email. A scammer sends you an email that appears (to the untrained eye) to be from Amazon, telling you that you must log into your account and change your password. If you follow the link in a phishing email, it will likely lead you to a fake Website (that looks semi-legitimate) where you will be asked to enter your username and password. Wi-Fi vs. cellular WiFi is close by and super-fast and cellular is virtually everywhere and sufficiently fast. WiFi comes from a wireless router, and cellular comes from cell towers, just like your cellular phone calls. WiFi (should) always require a password, whereas cellular just ‘works’ through your cellular provider (e.g. Verizon, T-Mobile). The cloud There are two main manifestations of ‘the cloud’: (a) services (like iCloud) that mirror (back up) what you have stored on your phone or your computer and (b) Google Docs. The main cloud services are iCloud, DropBox, OneDrive (which I do not recommend), Carbonite, and Google Drive. If you’re not a very powerful, famous, or beautiful person, the security risks of the cloud are more than offset by the convenience and redundancy (backup) benefits of the cloud. Google Docs is the other manifestation of the cloud, where you can create a document, spreadsheet, or presentation (the main things Microsoft Office includes) that resides only online, through a browser. Google Docs is free, can be used on almost any device, and has great redundancy, but it lacks the features and familiarity of Microsoft Office. Synchronization Synchronization is the cloud, but as it pertains to accounts, contacts and your calendar. You have true synchronization when your phone, your tablet, and your computer all have the same ‘living’ contact and calendar entries. So, when you enter a contact on your phone, you can edit it on your tablet or your computer and it will show up the same on all three devices. Another part of synchronization is when your smartphone keeps a backup of your accounts. So, if you lose or break your smartphone, Google (if you have an Android) or iCloud (if you have an iPhone) will allow you to be back in business much quicker when you get your new phone. IP address This is the most technical term in this list, but it’s also the most universal. All your devices have an IP address. You cannot use a computer on a network in 2019 without an IP address. You need an IP address to get on the Internet, and when you connect a wireless printer to your home network, it is ultimately done by your device (i.e., phone or computer) finding the wireless printer by its IP address. You don’t need to know much about this term other than it is a unique (but often changing) identifier for your device on a network. Being mildly familiar with these terms will help you be a more efficient, safe, and confident technology user. These core skills (above) are probably all you need to have to feel confident and safe using technology.
Most tech teaching is done as if you can learn something by being shown it once. Like in most areas of learning, you not only have to DO it yourself, but you have to do it 5 - 15 times before it sinks in. I also show you multiple ways of considering a technology problem (e.g. saving a file), so that you can adapt when weird things happen. Why I start with file management All technology is files. When you watch a YouTube video, you're downloading a (video) file to your browser. When your computer is infected with a virus, it is files that I -and the software tools I use- hunt for when I clean up the infection. When you get a new computer, one of the most important things is to get all your (personal) files from the old computer to the new computer. Even technology experts (including myself) struggle with file management. We all tend to have more data on our computers than we need, and in most ways, managing your digital data is like managing the clutter in our homes and our offices. In other ways, it's not like decluttering our physical world. In the physical world, big things (Old TVs) look big, whereas in the digital world, big things (video files) likely do not appear to be taking up more space on your hard drive. Also, in the physical world, when you intend to put an old TV in the corner of your garage, that's where it goes, whereas in the digital world, your computer will often put things in oddball places without telling you. The things you need to know about your files are:
Browsers, what are they? Google Chrome, Mozilla Firefox, Microsoft Edge, and Apple Safari and the most commonly used browsers. Your smartphone, your iPad also have browsers on them. If you visit a Website, you're using a browser. In fact, a browser is the ONLY program that can visit Websites. Now, you might say "But I can do Facebook either through a browser or through an app" and you'd be right. Some Websites also have an app, including Facebook, Pinterest, and the Wall Street Journal. Think of it this way: A browser is what you use to 'Google' something, like when a friend or family member makes a claim that you know is incorrect, you can verify it through a browser. What do I need to know about email? Email is the lifeline of the Internet. If all email services went down (in 2019), it would be a bigger deal than if all social networking went down. You need email to make reservations, buy tickets, get results of medical tests, create online accounts, and myriad other things. Regarding email, you need to know:
Until we have fingerprint scanners or better A.I. (artificial intelligence), we are all (including myself) stuck with keeping track of too many unique and complex passwords. This isn't really a technical skill you need to develop, but instead something we have to manage. I suggest using an alphabetized address book for your passwords. Some like password management programs like Roboform or LastPass, but I have personally found those to fail me about 15% of the time. End-user vigilance against security threats. Sadly, there is no 'set it and forget it' method to completely stop the bad guys from luring you into phishing or scareware scams. Phishing scams are fake emails that (a) get you to give away your credentials to nefarious parties or (b) visit a site that puts malware on your computer. Scareware is software (usually delivered through a hijacked browser) that displays fake or real threats to your computer. You need to be like a bouncer who can spot fake IDs or people who are already too drunk to let in to the nightclub. Thankfully, so far most phishing and scareware attempts are relatively easy to spot if you know what to look for. I charge $40/hr for tutoring and that includes materials such as guides and quizzes. Most who struggle with technology get help from (possibly younger) family, and that help usually wouldn't be called teaching. No offense to family; there are just certain subjects (e.g. driving a stick shift, cooking) that are better to hand off to an outsider. Some tech skills simply cannot be gained without a tutor, but that's only in the beginning. After a few sessions, you'll find that you CAN solve more of your own problems by googling them or watching a YouTube video. Call me if you want to gain the confidence you need to use technology more comfortably. What is a VPN?
Why are VPN's Useful?VPN's are useful because they hide what you are doing. Now, this doesn't mean that you are acting suspiciously, or you necessarily have something to hide. But the fact is that every time you look at something, every website you visit, every web page you pass by, will leave a tracking metric on your IP and target ads to you.
|
There are numerous VPN's to look at and it is hard to explain what you specifically value. We recommend things like PIA or NordVPN, but these are just because we've done the research and know what it would do to impact our internet connection.
|
Need help with Computer Security?
Most people won't check out internet security unless something has happened to prompt them to look in that direction. If you are looking for an internet security touch up or you are interested in some of our services, be sure to check us out via e-mail or give us a call!
Want to make your Phone even Better?
Our Top Five Apps to Download in 2019
CamScanner
|
Need Help with Your Android Phone?
If you are bored and just looking for some interesting stuff to do on your phone, we get that. But if you are having problems with your phone or have a cracked screen, be sure to give us a call and we can set you up in no time!
PC Vs Mac
We've briefly covered this topic in the past and the Mac is usually the better choice with some caveats. But we figured now would be a good time to go through each of the pros and cons in detail to ensure a solidified answer for you as an individual.
The fact is that PC vs Mac is a subjective debate. People on all sides are going to have their own opinions and it's up to us to cover those opinions in detail. But to summarize the answer in one sentence you're looking at: Buy Anew or Renew.
Addendum: This is purely talking about Desktops, not laptops.
The Benefits of a Mac - Buy Anew
Macs have a higher price point across the board. This is, for the most part, everything that Apple does is in-house. The software, the hardware, the programming, and the UI are all done through Apple so you have a consistent and stable product throughout.
|
The Benefits of PC - Renew
The benefits of the PC revolve around the fact that there are multiple entities working together to create a competitive marketplace for you. You can go out and build your own PC, upgrade your existing one, or just outright purchase an entire build for your PC.
The same goes for software, there are multiple different software for every product you could be looking for showcasing the fact that PC is all about choice.
Countless developers and manufacturers make it easy for you to choose the right thing. But with that, comes the need for information in something you might not want to get involved in.
The Cons of Mac
The price point of Mac is the biggest turn off for most users.
|
The Cons of PC
Open software can lead to people getting way in over their head. If you're not tech savvy, chances are you're not going to get the proper mileage out of this.
Some parts don't play well together. If you are building or upgrading a PC you need to look up guides online to ensure you're doing everything right. Luckily it's easy to contact the community but accidents can happen.
Viruses and Trojans. Now, this isn't as big of a problem as it used to be, provided you practice safe browsing methods and know the best antivirus that will work with you, but viruses and trojans are a thing and some of them watch what you are doing.
Microsoft tends to do dumb things (e.g., Windows 8) to their customers all the time and Apple tends to do offensive things (e.g., No headphone jack on new phones) to their customers occasionally.
Need Help Choosing?
If you are not tech savvy, chances are you're going to get more mileage out of a Mac. If you are looking for a good buy and know exactly what you're going to be using this for, then be sure to send us a message or give us a call, we can help you choose straight away.
What is G Suite?
G Suite is Google's Productivity suite for people who don’t want to pay a premium. Technically all of their Slides, Docs, Sheets, etc; are all part of the G Suite program. While this is free to everyone with a google account by default, it can be purchased at a premium ($5/$10 per month) for the 'business' version.
Is G Suite worth it for my Business?
The premium version of G Suite comes with a domain-oriented e-mail address, so brad@ctsmn.com would be included with the G Suite as well as a boost to the cloud storage of Google Drive from 10GB to 30GB (per user.)
|
G Suite vs. Office 365
The business versions of both of these products stack up almost identically, except for integration with Microsoft Outlook. Your odds of having Outlook synchronize (emails, contacts, calendars)properly are higher with Office 365 than with G Suite’s Outlook sync tool.
|
Need help with GSuite or Outlook?
Both of these suites come with 24/7 technical support but why would you call them when you can call someone who actually listens to you? If you are wanting to transition from one service to another or you are just ready to do something else, then give us a call. There are plenty of options on the table and we are ready to help you at a moment's notice.
Brad Copeland
Gentle, no-nonsense advice and perspectives on technology.